
Security
8
min read

Most Bitcoin lending platforms function on the "trust me bro" principle. Trust that your collateral is safe. Trust that it hasn't been lent out and rehypothecated. Trust that the code does what they say it does. BlockFi, Celsius, and Voyager asked for exactly that trust. You know how that ended.
Firefish was founded because its co-founders faced the same problem. "Martin had an investment opportunity but didn't have sufficient liquidity because part of his assets was in BTC. Both of us asked ourselves: how can we get a loan against BTC, minimizing counterparty risk?" says Igor Neumann, Co-founder at Firefish.
Two options existed: hand your Bitcoin to a centralised custodian and hope they gave it back, or wrap it in DeFi and introduce a different set of risks. Neither reflected how bitcoiners actually think about self-custody. So they built a third option.
Firefish is built for people who don't think trust is a security model. Here are five specific, verifiable layers protecting your Bitcoin.
Secured By Code, Not Custodians
There's a meaningful difference between a platform that says "we prioritise the security of your assets" and one that has built systems where mishandling those assets is cryptographically impossible. The first is a policy. Policies can be changed, ignored, or overridden under pressure. The second is an architecture. Architecture doesn't bend.
At Firefish, security isn't a feature added on top of a working product. It is the structure the product is built inside. Every design decision traces back to the same constraint: your Bitcoin should be unreachable by anyone who doesn't have the right to reach it, regardless of what anyone at Firefish says, does, or decides.
That constraint shapes everything. Here is how it plays out across five layers.
Layer 1: Non-custodial, 3-of-3 Bitcoin multisig escrow
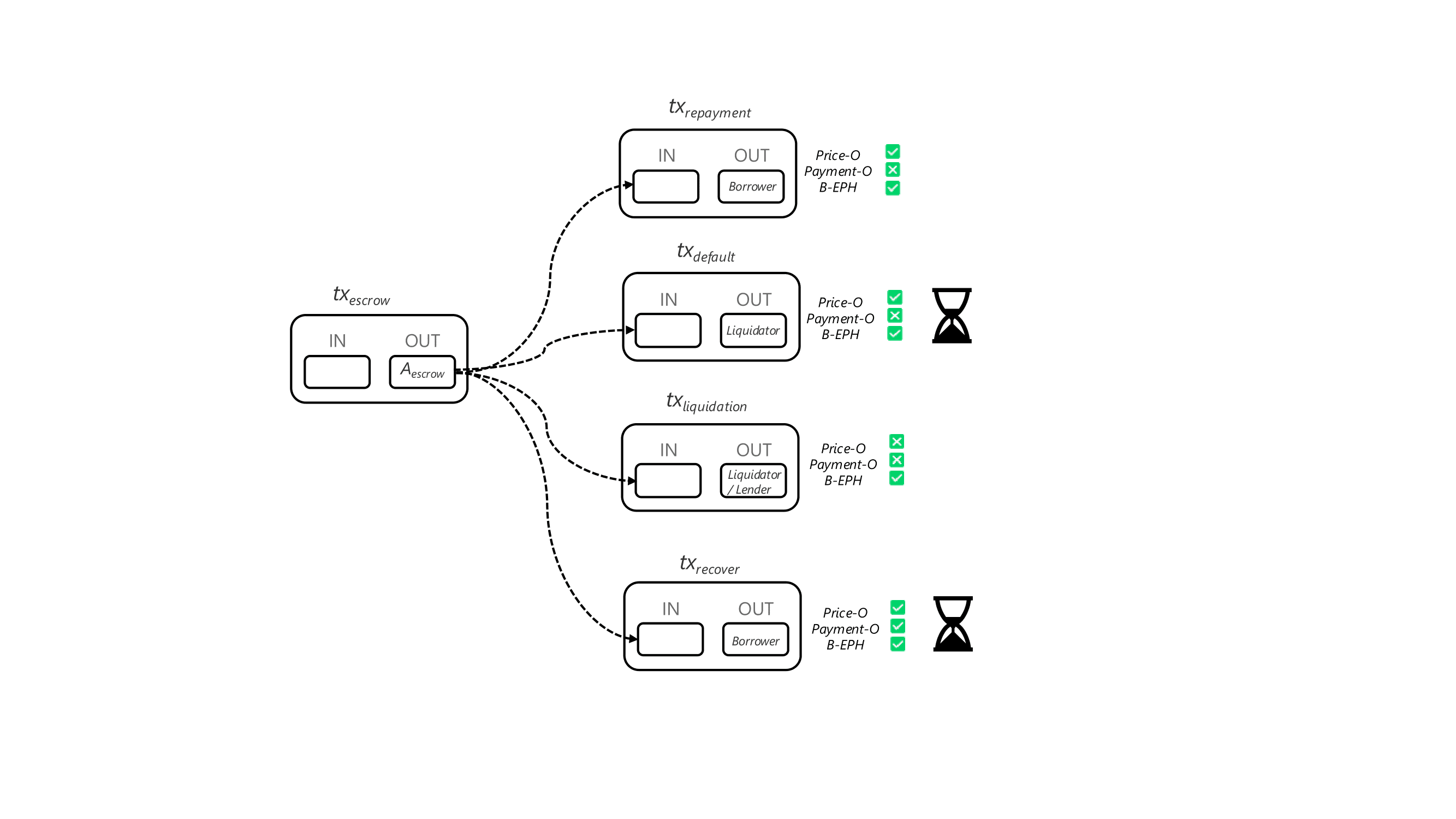
When a loan is created on Firefish, your Bitcoin moves into a 3-of-3 Bitcoin multisig escrow. Three keys are required to move it:
the borrower key,
the Price Oracle, and
the Payment Oracle. All three must sign.
The setup is iterative: the borrower pre-signs only the transactions that will actually occur, ensuring the oracles cannot create scenarios that weren't agreed to upfront. The oracles then pre-sign those same transactions. Your Bitcoin only moves once you've verified the setup is correct and there's no malicious configuration.
Every collateral movement happens on-chain. Only presigned transactions can ever execute. At any point, anyone can cryptographically verify their collateral sits in escrow, untouched. No rehypothecation. No trust required.
The relevance to 2022 is direct. Rehypothecation, the practice of lending out customer collateral to generate additional returns, was central to how Celsius and others collapsed. On Firefish, rehypothecation isn't against our policy. It's cryptographically impossible. There is no mechanism by which collateral sitting in escrow can be touched outside of the defined loan conditions. The escrow structure removes the possibility entirely.
For Bitcoin holders evaluating Bitcoin collateral loan security, this is the foundational question worth asking any platform: can the platform touch your Bitcoin without your key? On Firefish, the answer is no. Verifiably.
Layer 2: Public Source Code
The borrower protocol, the code that runs in your browser during a loan, is public source.
Anyone can read it. Anyone can inspect it. You can verify what it does with your Bitcoin before you use it. You are not being asked to trust our description of how the escrow works. You can check the code itself.
Here’s a walkthrough, where we prove that the Firefish borrower WASM binary published on the official site matches the public code repo.
The borrower protocol, the code running in your browser during a loan, is publicly auditable here.
Layer 3: Automated Scanning on Every Code Change
Before any new code ships, it is scanned by AISLE, automated security tooling integrated directly into our CI/CD pipeline. Not a yearly audit. Every single change, every time. AISLE is founded by former Avast CEO Ondrej Vlcek and researchers from Anthropic and Google. Their tooling uses LLMs to surface complex attack vectors that traditional scanners miss entirely.
It's a new paradigm in cybersecurity, and being on the defender side of that capability matters. This matters because periodic audits have a fundamental problem: they only cover what existed at the time of the audit. A vulnerability introduced the day after is invisible until the next one rolls around. Depending on the cadence, that window can be months. Continuous scanning means there is no window. Security review isn't a milestone we hit before a release. It's baked into how we write code in the first place.
Layer 4: Automated Testing and Production Monitoring
The Firefish protocol undergoes comprehensive architecture testing, and the production environment is monitored in real time. Build-time security and runtime security are both active and ongoing.
The goal of the architecture is to make the most serious failure modes structurally impossible. The goal of production monitoring is to catch anything unexpected before it has a chance to become a problem. These are not redundant. They cover different threat surfaces. Together they mean that security at Firefish is not something that was handled during development and then left to run. It is actively maintained.
Layer 5: Operations Security
Strong cryptography can still be undone by weak operational practices. Most security breaches don't start with broken code. They start with a compromised credential, a social engineering attack, or a single point of human failure.
At Firefish, the five layers above already minimize how much depends on human processes. But we close the remaining surface: FIDO2 hardware keys, encrypted disks, role-based access controls, and structured review across support and communication channels ensure issues surface fast and reach the right people immediately. The operation is lean and quickly reactive by design.
Layer 6: Rust Best Practices
Rust is the way.
“We picked the Rust programming language because it provides great tools for ensuring security and correctness while still being portable (runs basically anywhere). But we don’t stop at “just using Rust”. We actively design the code defensively using programming patterns such as new types with invariants, type state, immutability, making invalid states unrepresentable to squeeze maximum benefits of the language. These techniques can significantly decrease the chance of bugs and make it easier to prove various properties of the code.” - @Martin Habovštiak, Firefish Rust Developer
The track record
$160M+ in non-custodial Bitcoin lending facilitated. Nearly 5000+ BTC collateralized. 27,000+ users across 69 countries.
No security incidents.
That number reflects real volume across real market conditions, including the volatility that exposed the weaknesses in less carefully designed platforms. The architecture has been tested. It holds. The market has had years to find a flaw. It hasn't.
”Firefish puts security at the core of its development process - systematically minimizing risk on multiple levels to catch problems as early in the pipeline as possible at the right cost of time and effort. Making sure we can move fast without breaking things,” says Adam Pazderka from the tech team at Firefish.
What This Means for Bitcoin Holders Considering a Bitcoin-Backed Loan
The right question to ask any Bitcoin lending platform is not "does this seem trustworthy?" Trust is what you extend before the architecture exists. Architecture is what you verify when trust on its own isn't enough.
At Firefish, the collateral escrow is verifiable on-chain. The borrower code is readable by anyone. The review process is documented. The track record is public. None of these things require you to take our word for anything.
For Bitcoin holders who lived through 2022, or who watched it from the sidelines and drew the obvious conclusions, the due diligence checklist is well established: who holds the keys, can the platform touch your collateral, is the code reviewable, and does the platform have a clean track record under real conditions. Firefish has a specific, verifiable answer to each of those questions.
Never sell your Bitcoin. Live off it.



